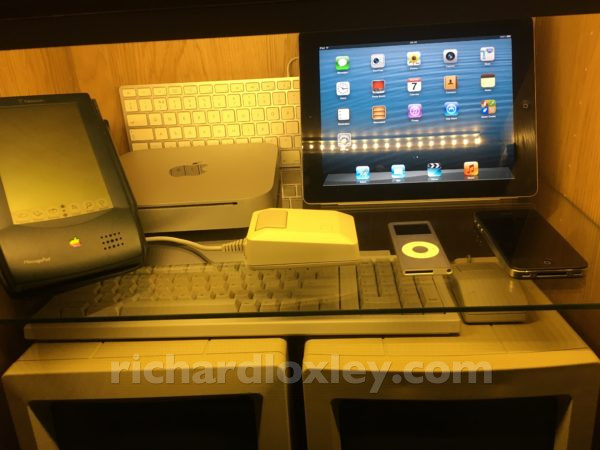
I collect old computers, and so my friends often find interesting things for my collection. My friend Paul recently gave me an old iPad 2 for my museum.
The thing is, it didn’t feel very old. I still use an iPad 3 every day as my main tablet (it still works fabulously well, apart from the bloat on modern web pages, that sometimes tend to cause Safari to grind to a halt). The donated iPad 2 ran iOS 9.3.5 (very slowly), which is basically what my iPad 3 runs (iOS 9.3.6 due to last year’s GPS bug that Apple patched).
So to be a candidate for my museum I really wanted to revert it to its original state, which would have been iOS 4. But Apple don’t allow downgrades, and all installs of iOS have to be cryptographically signed by Apple.
So I set about seeing if jailbreaking the iPad would help. Apparently not – jailbreaking on its own doesn’t bypass the iOS signing.
But I found a few references to iOS 6.1.3. It seems this was the first version of iOS to allow OTA (Over The Air) updates to iOS. So Apple allowed 6.1.3 to be manually installed via USB (so that devices running earlier versions could update, and then update to the latest version over the air).
So I tried a few versions of this – first using a Windows tool (3utools) – which failed with an obscure error, and then using iTunes on a Mac (having downloaded iPad2,1_6.1.3_10B329_Restore.ipsw from https://ipsw.me/iPad2,1) – which revealed that Apple wouldn’t sign it any longer. That corrupted the device so I was forced to reinstall 9.3.5 using iTunes.
Doing a bit more reading, it seemed Apple had stopped signing 6.1.3 a few months ago, possibly due to a security bug in iCloud on iOS 6 that they wanted to avoid being exploited? Details were a bit vague.
Then I found some references to them still signing OTA updates to 6.1.3, just not manual updates via IPSW files. The tool Vieux promised to be able to downgrade to iOS 6.1.3 or 8.4.1. Again the description is vague, but I think it’s installing the update from the IPSW file, but persuading Apple that it’s an OTA install to fool them into signing it? I’m not exactly sure – there is never much deep technical documentation on these hacking tools – the authors seem to think everyone just wants tools that are easy to use, so don’t often explain how they work!
Vieux looked promising, but for 32bit systems like my iPad 2, it required ssh access, which requires a jailbreak!
So next, find a jailbreak for iOS 9.3.5. It seems there is only one that works: Phoenix. It’s an app that you ‘side load’ onto your device, and after each boot, you manually run it to activate the jailbreak. Any app loaded has to be signed by Apple, and there were various webpages promising versions of Phoenix already signed, but Apple revokes the certificate as soon as they find them, so they don’t last long.
The alternative is various tools that you can use to sign the app yourself. Anyone can sign their own app for development purposes, but the certificate only lasts 7 days. Or if you have a developer account (as I do), you get a year until you have to re-sign and re-install it.
Reading forums, it seemed many tools that previously did this (3utools, Cydia Impactor) no longer worked.
I did try a tool called iOS App Signer, which should have signed an app using my developer certificate for a full year of use, but I couldn’t get the signed app to install on the iPad, whatever certificate or settings I used. I gave up on that (but see below for a possible reason).
Then I found a couple of tools AltServer and AltDeploy. They seem similar. AltDeploy just signs an app with a 7 day certificate based on an iTunes account and installs it to your device. AltServer does the same, but then runs a server on your computer so your jailbroken device connects to your computer via wifi, and requests a new version before the 7 days run out.
Both of them install a rather dodgy plugin. It might make sense, but the developers don’t explain why. It’s a plugin to the Mail app on your Mac, which they say has to be installed, and Mail running, for the app signing to work (they say it’s something to do with requesting your iTunes credentials). A bit more explanation wouldn’t go amiss. I eventually allowed it access (since I don’t use Apple’s Mail app for my email anyway, so there’s nothing useful to hack there).
I then used AltDeploy to sign the Phoenix app. This also failed, but this time I got an error that I could search for (a bad app display name). It seems the Phoenix app uses extended characters in the app name (to join the o and e characters together). The app signing didn’t like that. Perhaps that’s also why iOS App Signer didn’t work? I didn’t go back to check.
Anyway, this issue suggested changing the Phoenix5.ipa filename to .zip, expanding it, opening the Payload folder, showing the package contents, editing Info.plist, changing the Bundle Display Name to remove the dodgy character, saving, re-zipping the Payload folder, and renaming back to .ipa. Then the signing worked, and I had the Phoenix jailbreak app on my iPad!
I followed the instructions to activate it, then kickstart it, then opening Cydia and installing ssh.
Next get the dependencies for Vieux:
cd /Users/Richard/Desktop/Vieux-master Mac-Pro:Vieux-master Richard$ pip3 install -r requirements.txt Collecting bcrypt==3.1.7 (from -r requirements.txt (line 1)) Downloading https://files.pythonhosted.org/packages/62/20/4c94f3f8dfc6b8720c8bc903ce2951ec6397ad864e3a64b4abdced014514/bcrypt-3.1.7-cp34-abi3-macosx_10_6_intel.whl (53kB) |████████████████████████████████| 61kB 1.8MB/s Collecting bsdiff4==1.1.9 (from -r requirements.txt (line 2)) Downloading https://files.pythonhosted.org/packages/39/34/bd2ae6cd4b2a5d3af9173a9d7f6ecd2723ea7b0401ad807a0c7e7b50faa3/bsdiff4-1.1.9.tar.gz Collecting cffi==1.13.2 (from -r requirements.txt (line 3)) Downloading https://files.pythonhosted.org/packages/d5/61/32b1aa5ef1bf60be4ef679c4aae082a7ceef98517e0e0fde68072c6ef8b6/cffi-1.13.2-cp37-cp37m-macosx_10_6_intel.whl (258kB) |████████████████████████████████| 266kB 5.5MB/s Collecting cryptography==2.8 (from -r requirements.txt (line 4)) Downloading https://files.pythonhosted.org/packages/6b/4a/ce93178469d4460d6b3a5e648fc1a2f426030f3d30a12d7ed4df73d044de/cryptography-2.8-cp34-abi3-macosx_10_6_intel.whl (1.6MB) |████████████████████████████████| 1.6MB 6.4MB/s Collecting paramiko==2.7.0 (from -r requirements.txt (line 5)) Downloading https://files.pythonhosted.org/packages/1c/d8/50243699d41d6eabd19efb86fb00d99f89580e5cb795b577a5c32ce39ae7/paramiko-2.7.0-py2.py3-none-any.whl (206kB) |████████████████████████████████| 215kB 12.1MB/s Collecting pycparser==2.19 (from -r requirements.txt (line 6)) Downloading https://files.pythonhosted.org/packages/68/9e/49196946aee219aead1290e00d1e7fdeab8567783e83e1b9ab5585e6206a/pycparser-2.19.tar.gz (158kB) |████████████████████████████████| 163kB 8.7MB/s Collecting PyNaCl==1.3.0 (from -r requirements.txt (line 7)) Downloading https://files.pythonhosted.org/packages/cd/c9/4d6deea9d900345b1243cc3e6265110697fae5e594689cfa1ba34e0ef4a8/PyNaCl-1.3.0-cp34-abi3-macosx_10_6_intel.whl (284kB) |████████████████████████████████| 286kB 6.1MB/s Collecting pyusb==1.0.2 (from -r requirements.txt (line 8)) Downloading https://files.pythonhosted.org/packages/5f/34/2095e821c01225377dda4ebdbd53d8316d6abb243c9bee43d3888fa91dd6/pyusb-1.0.2.tar.gz (54kB) |████████████████████████████████| 61kB 7.9MB/s Collecting scp==0.13.2 (from -r requirements.txt (line 9)) Downloading https://files.pythonhosted.org/packages/4d/7a/3d76dc5ad8deea79642f50a572e1c057cb27e8b427f83781a2c05ce4e5b6/scp-0.13.2-py2.py3-none-any.whl Collecting six==1.13.0 (from -r requirements.txt (line 10)) Downloading https://files.pythonhosted.org/packages/65/26/32b8464df2a97e6dd1b656ed26b2c194606c16fe163c695a992b36c11cdf/six-1.13.0-py2.py3-none-any.whl Building wheels for collected packages: bsdiff4, pycparser, pyusb Building wheel for bsdiff4 (setup.py) ... done Stored in directory: /Users/Richard/Library/Caches/pip/wheels/97/14/f1/8ecc06baa54bcc9b282b073673b1e1197f894c32942446a6ea Building wheel for pycparser (setup.py) ... done Stored in directory: /Users/Richard/Library/Caches/pip/wheels/f2/9a/90/de94f8556265ddc9d9c8b271b0f63e57b26fb1d67a45564511 Building wheel for pyusb (setup.py) ... done Stored in directory: /Users/Richard/Library/Caches/pip/wheels/1f/a9/7e/d189b5030ee3a56f9b72c28281bb11d661b8ea312e28de08a5 Successfully built bsdiff4 pycparser pyusb Installing collected packages: six, pycparser, cffi, bcrypt, bsdiff4, cryptography, PyNaCl, paramiko, pyusb, scp Successfully installed PyNaCl-1.3.0 bcrypt-3.1.7 bsdiff4-1.1.9 cffi-1.13.2 cryptography-2.8 paramiko-2.7.0 pycparser-2.19 pyusb-1.0.2 scp-0.13.2 six-1.13.0
I could then plug in the iPad via USB and downgrade:
./vieux -i ~/Desktop/iPad2,1_6.1.3_10B329_Restore.ipsw
/(//* /
/(%@&/*((//*/
(((((* %(&@@(*,///
((,((((((((/%%/,/(///
((((((((/*.((((////////**
(((((((((((((((((///////**.
((((((((((((((((//////*** .
((((((((((((((//*//(%#(/*..
(((((((((((////** /%%#(* .
(////////////**..##(/* ..
*(/*******,,,,...,* ,...***.
*(((&@@*.......*/***/////(//*////
*** /((#@@@@@@@@@@@@@@@(///(((/**/*///
#&(***/((%@@@@@@@@@@@@@@@(/((((// *****
((((%(*/((#@@@@@@@@@@@@@@@@((((//****
(((((////(&@@@@@@@@@@@@@(((((//*,,,,
((((.//* %&&@@&&@@&((((////,.,,/((*
(((/* **(%%&&&&&&&((((//**/** ((//
(((((* ./##%%%%#((///**#&*******
/((* */(((/****/(((((#(**
*(((((((
(((((((*
*((((((*
(((((
Vieux - A tool for 32/64 Bit OTA downgrades
Current version is: 1.0.1
If you are using a 64 Bit device then connect it in DFU Mode
If you are using a 32 Bit device then just have it connected in NORMAL mode
Files cleaned.
/Users/Richard/Desktop/iPad2,1_6.1.3_10B329_Restore.ipsw is a zip archive!
Starting IPSW unzipping
Continuing...
IPSW found at given path...
Cleaning up old files...
Files cleaned.
Unzipping..
Unable to get SEPNonce from lockdownd
NOTE: Unable to get SepNonce from device
Starting iBSS/iBEC patching
Looks like you are downgrading an iPad2 to 6.1.3!
Please enter your devices IP address (Find it in WiFi settings):
10.0.0.75
Please enter the root password to your device (Default is 'alpine'):
Connecting to device via SSH...
Device is not running iOS 10.x, using normal TFP0 kloader...
Please press the home button on your device or unplug and replug it back in.
Waiting 10 seconds for you to do this.
Getting SHSH...
Restoring...
Note that errors about 'BbSkeyId', 'FDR Client', 'BasebandFirmware Node' and 'ERROR: zip_name_locate: Firmware/all_flash/manifest' are not important.
Just ignore them and only report errors that actually stop the restore.
ERROR: Unable to connect to FDR client (-2)
ERROR: Failed to start FDR Ctrl channel
Files cleaned.
Finished! Enjoy your downgraded device :)
(When prompted you have only 10 seconds to unplug the USB lead and reconnect it!)
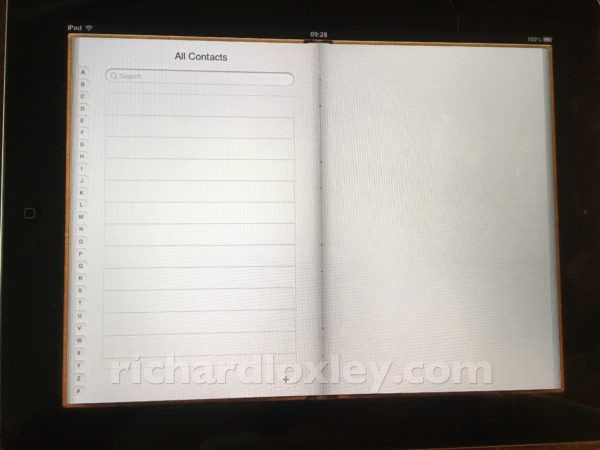
After I did that, I had a factory-reset device running iOS 6.1.3. It seems to be stock iOS, signed by Apple with no jailbreak (although I believe there are iOS 6 jailbreaks that could be installed). But I want it nice and clean, for my museum :-)
Here’s some useful links for what I used that worked:
- AltDeploy: https://github.com/pixelomer/AltDeploy
- Tutorial for AltDeploy: https://kubadownload.com/news/altdeploy-sign-ipa-files
- Tutorial for using AltDeploy to install Phoenix: https://kubadownload.com/news/phoenix-jailbreak
- Phoenix jailbreak: https://phoenixpwn.com/
- How to fix the app name issue in Phoenix: https://github.com/pixelomer/AltDeploy/issues/56
- Vieux tool to downgrade iOS: https://github.com/MatthewPierson/Vieux
- Downloads for old versions of iOS (ignore the warnings about not being able to sign them if using Vieux for iOS 6.1.3/8.4.1/10.3.3 on compatible devices as it will take care of the signing): https://ipsw.me/
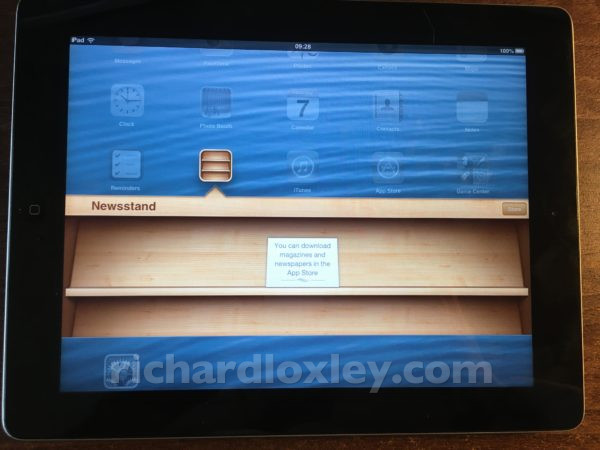
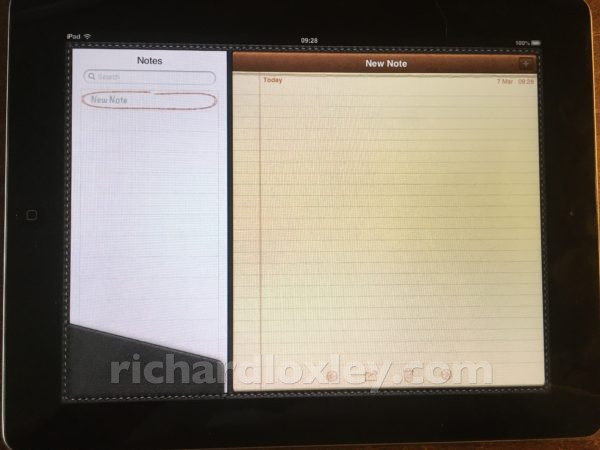
Check out that retro skeuomorphic design! It’s not quite the original iOS 4, but visually it’s almost the same, as the flat design didn’t come in till iOS 7.
And now it truly is a museum piece :-D